Google boasted that its current Chrome OS has better security features than the latest Windows and macOS versions. This simply means that Chromebook can efficiently protect your sensitive data against some malicious files.

"Chromebooks are designed to protect against phishing and ransomware attacks with a low on-device footprint, read-only, constantly invisibly updating Operating System, sandboxing, verified boot, Safe Browsing, and Titan-C security chips," said Google experts.
Google also explained that its Chrome OS can help reduce the vulnerabilities of various organizations' systems. If this is true, then those people who heavily rely on a browser to do online tasks can definitely benefit from Chrome OS.
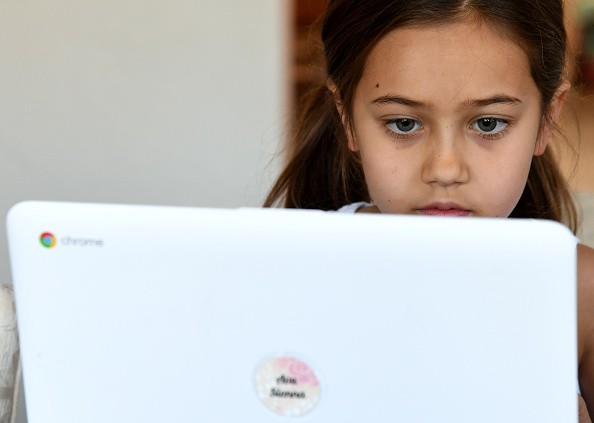
Google Chromebooks are Now Being Adopted
According to Forbes' latest report, various schools, universities, companies, and organizations are now adopting Google's popular laptop model.
On the other hand, many school authorities also claimed that they trust Chromebooks compared to other laptop brands, especially when it comes to protecting their systems.
Also Read : Google to Stop Slanderous Websites from Roaming the Internet - Here's What You Need to Know
Aside from confirming that Chrome OS can efficiently protect your information, Google also released a new blog, which offers new methods on how to prevent a ransomware attack.
These techniques could attract many companies, especially now that various hacking groups were able to breach iConstituent, JBS, and other giant companies. To give you more ideas, here are the details of Google's latest blog.
Google's Anti-Ransomware Measures
In Google's latest blog, the search engine giant disclosed five important methods to prevent ransomware breaches. If your company doesn't have enough budget to buy security tools or hire security experts to improve your systems, then you can use these five techniques:
- PROTECT: Create safeguards to ensure the delivery of critical services and business processes to limit or contain the impact of a potential cybersecurity incident or attack.
- RESPOND: Activate an incident response program within your organization that can help contain the impact of a security (in this case, ransomware) event.
- IDENTIFY: Develop an understanding of what cybersecurity risks you need to manage for the scope of your assets, systems, data, people, and capabilities.
- DETECT: Define continuous ways to monitor your organization and identify potential cybersecurity events or incidents.
- RECOVER: Build a cyber resilience program and backup strategy to prepare for how you can restore core systems or assets affected by a security incident.
For more news updates about Google and its upcoming anti-ransomware innovations, always keep your tabs open here at TechTimes.
This article is owned by Tech Times
Written by: Griffin Davis
ⓒ 2026 TECHTIMES.com All rights reserved. Do not reproduce without permission.




